Anatomy of a rule
The filtering behavior of Little Snitch is defined by a set of rules. A rule consists of four parts:
- Condition
- Identity check
- Action
- Other properties
If a connection attempt matches the condition of a rule and the identity check is successful, the rule’s action is performed. If more than one rule matches a particular connection attempt, the one with the highest precedence is used.
Condition properties
The condition properties of a rule define by which condition the rule matches a connection. They are analogous to their connection counterparts.
Connect direction
A rule can match either outgoing or incoming connections. An outgoing connection is when a process on your computer initiates a connection to somewhere else. In the metaphor of the phone call, your computer dials a phone number to call somebody else. An incoming connection, on the other hand, is when a remote computer initiates a connection to a process on your computer. Your computer acts as a server in this case. In the metaphor of a phone call, this is when your phone rings and you accept a call.
Process
A process is an application (an “app”) with a graphical user interface, a background process (Unix daemon) needed by the system to perform certain tasks (e.g. sync your data to the cloud) or a Unix command with no graphical user interface. Processes are matched by their file system path (where they are stored on your disk).
Applications may execute Unix commands to do things on their behalf. If Little Snitch encounters a Unix command which has been started by an Application, it shows both the Unix command and the Application, e.g. "Terminal via ping". Rules matching the application will match this combination as well. However, you can also create rules which match a particular combination of application and Unix command only (via-rules).
Process owner
Processes have an owner. The owner is usually the user who started the process. This user can also be the operating system (denoted as “System” by Little Snitch). Processes started by a user can gain system privileges by asking for an admin login.
Processes owned by the system are often of particular importance because they provide services for all users on the computer, not just for you. Rules matching processes owned by the system are therefore global, they are shared by all users. To handle various tasks, the system uses many different users that Little Snitch all considers system users. These are essentially all user accounts with user IDs below 500, except 201 (guest user) and -2 (nobody).
When Little Snitch shows a connection alert for a system process, it prepends the process name with a gear wheel icon:
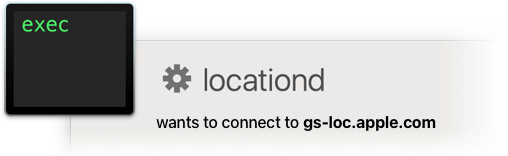
The same icon is used to flag rules matching system processes only.
In addition to matching processes owned by the current user (“me”) and the system, Little Snitch rules can also match processes owned by anyone. These rules are called global rules, show up in all users’ rule sets and also match processes owned by the system. Since rules of this type have an effect on all users, the permission to create them must be enabled in Little Snitch Configuration. Open Little Snitch Configuration > Preferences > Security and turn on Allow Global Rule Editing.
Server (remote computer)
This property can be one of:
- A list of domains — Matches remote computers where Little Snitch knows the name and the name is in any of the domains listed.
- A list of hostnames — Matches remote computers where Little Snitch knows the name and the name is listed exactly.
- IP addresses — Matches remote computers with an Internet address listed in this option or in one of the ranges listed. The list can contain individual IPv4 and IPv6 addresses and ranges of these addresses. A range is denoted by two addresses separated by a dash (minus-) character.
- Local network — Matches computers on private networks, Bonjour addresses and Broadcast addresses. Usually these are your printer, your router and other computers in your house. But be careful: In an Internet Café, it matches also the computers of all the other people in the café.
- Broadcast addresses — Matches an address in your local network which is used for broadcasts. Messages sent to this address can be received by all computers in the network. Primarily used to find resources in your local network.
- Bonjour addresses — Similar to Broadcast Addresses, used to find resources in your local network.
- Multicast addresses — Matches Internet addresses in a particular range which is used to send data to multiple computers not necessarily in your local network.
- DNS servers — Matches connections to the Domain Name Servers currently configured for your computer.
Learn more about the Domain Name System… - Berkeley Packet Filter — The Berkeley Packet Filter is a low level service of the operating system which can be used to eavesdrop all network communication of your computer or even other computers in your network. It can also be used to inject and receive any type of network packets.
While all of these options can be used to match outgoing connections, incoming connections cannot be matched by name or domain because the remote name is never known reliably.
Protocol
A rule can match on particular protocols only (usually TCP, UDP or ICMP) or on any protocol.
Port
Some protocols have a port number for each end of the connection. For outgoing connections, the rule matches if its port matches the connection’s remote port. For incoming connections, the rules’s port must match the local port where the connection is accepted.
Rules can match either a single port or a range of port numbers (e.g. 137-139) or any port.
Profile
A rule may be effective only when a particular profile is active. If this property is not set, the rule is effective in all profiles. Although this property has no connection counterpart, it is part of the condition which the rule matches under.
Enabled
Rules can be enabled or disabled. Disabled rules never match, they behave as if they had been deleted. However, the information stored in the rule is not lost. The rule can be re-enabled at any time. This property is particularly useful for protected rules (they cannot be deleted) or if you want to test what effect it would have if a particular rule were deleted.
Identity check properties
If the condition properties of a rule match the connection attempt, the connecting program's identity is checked. Allow-rules are only applied if the identity check succeeds. If it fails, an alert with a warning is shown. The check is based on the following properties:
- Type of check to perform (determines the interpretation of the latter two properties).
- Identification of the developer.
- Identification of the program in the scope of the developer.
See section Process identity checks for more details.
Checking Any Process rules
Rules matching Any Process cannot check the program's identity, because there is no particular identity to check for. Instead of checking for a particular identity, Little Snitch can (optionally) check whether the program is “trustworthy”. But what makes a program trustworthy? Little Snitch defines it this way: A program is trustworthy, if it has a valid code signature with a certificate chain originating at Apple's root certificate. It guarantees that the identity of the developer responsible for the program can be determined.
Action
A rule’s action defines what shall be done when the condition properties of the rule match a connection. It can be either Allow, Deny, Ask or Private. If the action is Ask, Little Snitch behaves basically as if no rule had matched. It prevents rules with lower precedence from matching and a connection alert is shown (unless Silent Mode is active).
Rules with the action Private have no effect on the network filter. They determine whether individual connection statistics are collected by Network Monitor. If a rule with the action Private matches, Network Monitor adds statistics to an item named Private Connections, not revealing the remote server name, Internet address or other connection data.
Other properties
Lifetime
Rules can be set to expire at a particular time or event. This property describes when the rule expires. Possible options are:
- Never, the rule is permanent.
- When the process quits.
- When user logs out.
- When the system restarts.
- After a period of time.
Priority
If this property is set, it lifts the rule’s precedence over all other rules that don’t have one. We recommend that you use priority rules sparingly and only in profiles.
Notes
You can add a note to every rule, e.g. describing the purpose of the rule. Factory rules come with a description of the rule’s purpose. Rules created via connection alert or Network Monitor get a note with a summary of the connection shown in the alert or in Network Monitor by default. You can edit factory descriptions and automatically created descriptions at will.
Creation date
Automatically set when the rule is created.
Protected
Protected rules cannot be edited, but they can be disabled. Little Snitch Configuration uses a lock icon to indicate a protected rule.
There are two kinds of protected rules:
- Factory rules — These rules are part of the factory rule set. They are crucial for your system to work properly. You can disable them. This is only advised if you know what you are doing.
- Rule groups — These rules are maintained and published by someone else and updated over the Internet. Subscribers can not edit them.
Unapproved
Rules created outside of Little Snitch Configuration are tagged as unapproved. As a preferences option (preferences section Advanced), rules created via connection alert or Network Monitor can be set to be approved right away. To approve a rule, right-click it and choose Approve from the context menu. If the preferences option Approve rules automatically (also in the same section) is active, rules are approved by simply selecting them.
War dieser Eintrag hilfreich? Hinterlass uns Feedback.
© 2016-2026 Objective Development Software GmbH